Some time in the last few days, Gregory Evans or one of his employees at High-Tech Crime Solutions (HTCS) fell victim to a simple phishing scam. The attack works when a compromised Twitter account starts sending out direct messages (DMs) to followers. The message uses a variation on a message that implies someone is saying "terrible things about you", and provides a link to click to see it. In reality, that link takes the person to a page that looks like Twitter and requests Twitter login information to proceed. Once the person types in their Twitter account credentials, their account is hijacked and used to further spread the attack.
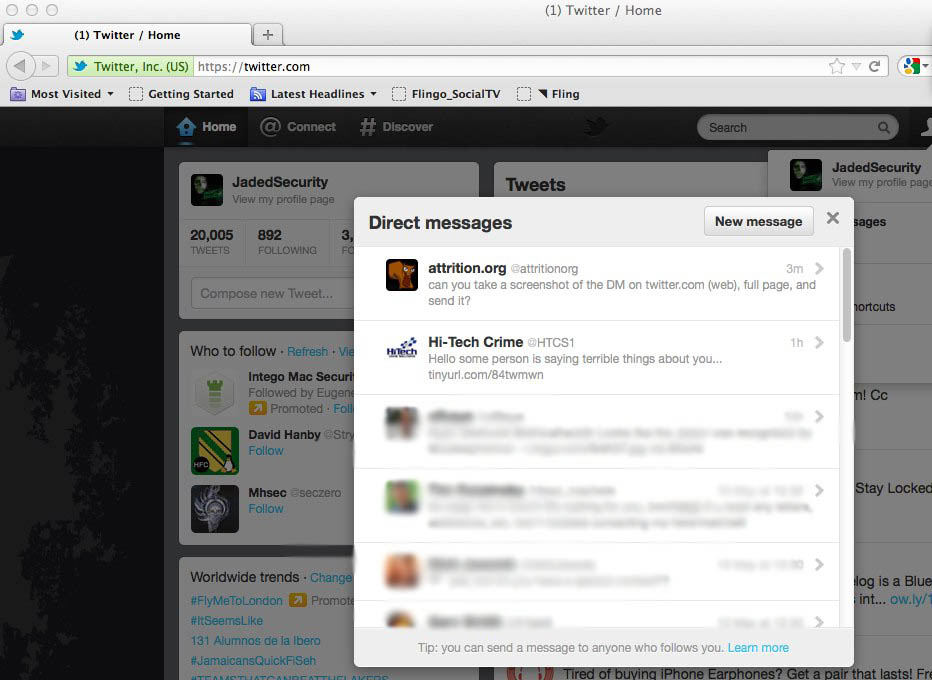
While this attack is relatively new to Twitter, it is a classic phishing attack that any security professional should be aware of. This particular attack has been covered by Techie-Buzz and even Oprah's web site. Despite that, ironically enough, Evans' "Hich-Tech Crime Solutions" fell victim. When the @HTCS1 account started sending out direct messages, people quickly realized what happened. The screenshot below clearly shows the compromised account in action:
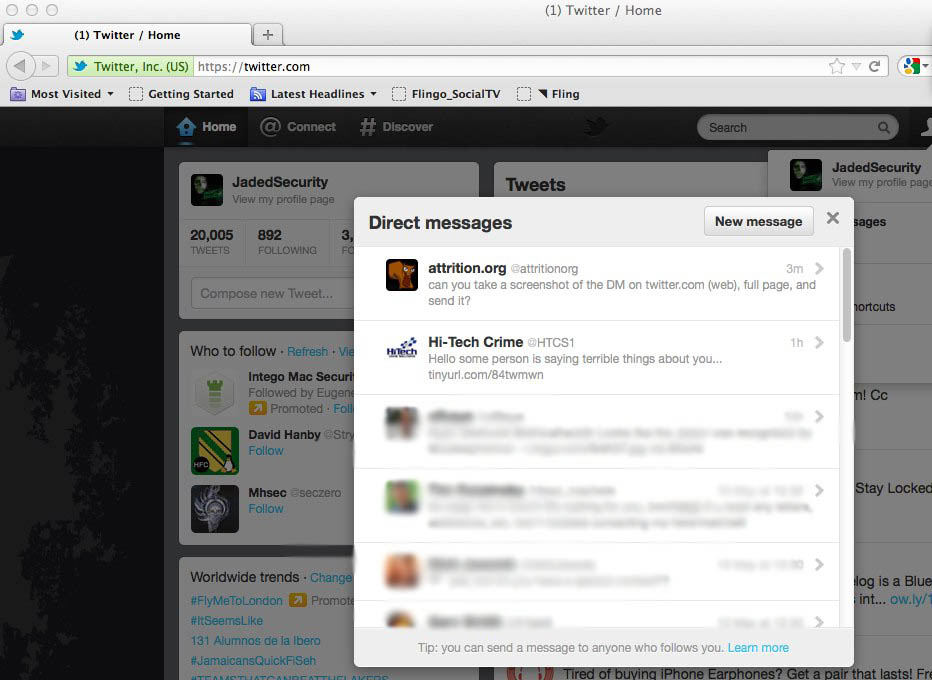
Even worse than getting phished in this manner, is that HTCS is simply denying that the account sent DMs, when it clearly did. They either do not understand how the hack works, or do not understand the basics of Twitter including direct messages:

Note that three hours after Evans said they were working on it, the account was still compromised and sending out spam. That means that in that time, Evans could not figure out how to use the Twitter interface to revoke the permissions from the application that was controlling the account.
As always, if you receive a direct message with wording implying someone is saying "terrible things", don't follow the link. For more variations of the message, this page has documented them as well as the quick solution to the problem; and it isn't very high tech.